What are Corporate Investigations?
Definition and Scope
Corporate investigations involve a comprehensive examination into a company's operations, finances, and behavior to uncover fraud, misconduct, or other nefarious activities. These investigations are designed to scrutinize various aspects of the business to ensure everything runs smoothly and legally. From financial audits to behavioral scrutiny of employees, a corporate investigation can cover all areas of concern within a company.
Corporate investigations are not just confined to discovering fraud or theft. They also play a pivotal role in uncovering regulatory violations, unethical behavior, and breaches in corporate policy. Through these investigations, companies can identify areas of risk and take necessary corrective measures.
- Examination of financial records to identify discrepancies.
- Monitoring of employee behavior and practices.
- Ensuring compliance with local, state, federal laws, and regulatory compliance.
- Investigating potential regulatory violations and ethical breaches.
- Suspicions of internal theft or fraud.
- Evidence of embezzlement or financial misconduct.
- Potential intellectual property infringements.
- Investigating allegations of harassment and discrimination.
- Addressing substance abuse issues in the workplace.
- Ensuring a positive and safe work environment.
- Upholding the company's values and ethics.
- Protecting the company from lawsuits and damages.
- Safeguarding intellectual property rights.
- Protecting proprietary information from theft.
- Ensuring the company's competitive edge.

Objectives
The main objectives of corporate investigations are to protect company assets, ensure compliance with laws and regulations, and uphold ethical standards. By doing so, corporations can safeguard their reputation and maintain a trustworthy image among stakeholders, clients, and the public.
Ensuring adherence to legal standards and ethical guidelines is crucial for any business. These investigations aim to identify any malpractices and resolve them to prevent future occurrences. This not only ensures the integrity of the company but also helps in retaining the trust of employees and partners.
- Protecting physical and intellectual assets.
- Ensuring compliance with regulatory frameworks.
- Upholding ethical and moral standards within the organization.
- Identifying and mitigating potential risks.
Common Triggers
Investigations are often initiated due to suspicions or evidence of employee theft, fraud, embezzlement, intellectual property theft, or regulatory violations. Such occurrences can significantly damage the company's reputation and finances if not addressed promptly and adequately.
Understanding the triggers for these investigations is crucial for preventing significant threats to a company. By identifying the common causes, businesses can implement preventive strategies and protocols to minimize risks effectively.
- Suspicions of internal theft or fraud.
- Evidence of embezzlement or financial misconduct.
- Potential intellectual property infringements.
- Violations of regulatory guidelines and compliance
Key Players
These investigations are typically conducted by corporate security teams, internal auditors, or external private investigators specialized in corporate matters. Their expertise ensures a thorough and impartial inquiry into the issues at hand.
Corporate investigators bring a wealth of experience and skill to the table, ensuring detailed and credible investigations. Their specialized knowledge allows them to uncover hidden issues and provide actionable solutions to the company.
- Corporate security teams oversee internal security threats.
- Internal auditors ensure financial records' accuracy.
- External private investigators bring an objective viewpoint.
- Legal experts ensure compliance with laws and regulations.
Methods and Techniques
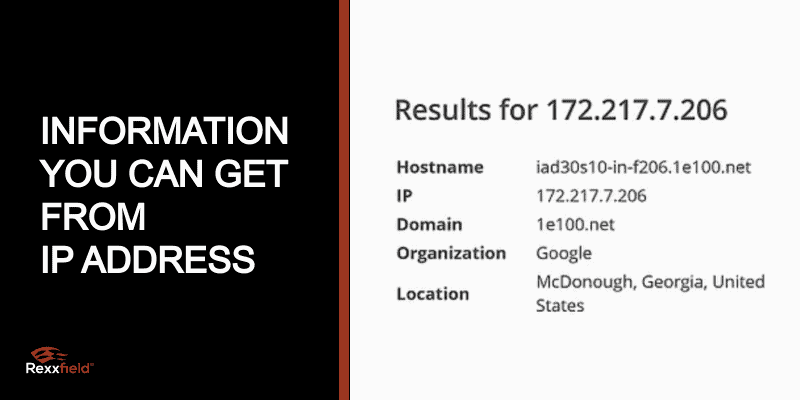
Techniques used can include surveillance, forensic accounting, background checks, digital forensics, and interviews with employees and associates. Each method provides a unique perspective on the investigation, ensuring a well-rounded approach to uncovering the truth.
These methods allow investigators to gather comprehensive evidence and insights into the issue. Utilizing modern tools and techniques ensures accuracy and effectiveness in identifying and addressing corporate misconduct.
- Surveillance to monitor suspicious activities.
- Forensic accounting to audit financial records.
- Background checks on employees and associates.
- Interviews to gather firsthand accounts and testimonies.

Corporate Investigation Examples
Employee Misconduct
Corporate investigations frequently address issues such as employee theft, fraud, or violations of company policy. These investigations help in maintaining a trustworthy and ethical workplace, ensuring employees adhere to the company's guidelines.
Addressing employee misconduct is vital for creating a positive work environment and reducing conflicts within the company. Investigations help identify individuals involved in unethical behavior and take necessary disciplinary actions against them.
- Investigating cases of employee theft and fraud.
- Addressing violations of company policy effectively.
- Ensuring adherence to company guidelines.
- Maintaining a trustworthy and ethical workplace.
- Reducing conflicts and promoting harmony among employees.
Due Diligence
Another common type of investigation involves conducting thorough background checks on potential business partners, investors, or acquisition targets to ensure compliance and reliability. Due diligence ensures that companies make informed and strategic decisions.
Background checks are essential in forging reliable business relationships. Thorough investigations during due diligence help companies avoid partnering with unreliable or dishonest entities, thus safeguarding their interests and future prospects.
- Conducting background checks on potential partners.
- Ensuring compliance and reliability of associates.
- Making informed and strategic business decisions.
- Safeguarding company interests and future prospects.
- Avoiding partnerships with dishonest entities.
Intellectual Property Protection
Investigations that focus on identifying and mitigating risks related to the theft or misuse of a company’s intellectual property, such as patents, trademarks, and proprietary information, are also prevalent. Protecting intellectual property is crucial for maintaining the company's competitive advantage.
Intellectual property theft can significantly damage a company's market position and revenue. Corporate investigations help identify potential threats and take measures to protect valuable intellectual assets, ensuring the company's long-term success.
- Identifying threats to intellectual property rights.
- Mitigating risks of intellectual asset theft.
- Protecting patents, trademarks, and proprietary information.
- Maintaining a competitive advantage in the market.
- Ensuring long-term success and stability of the company.
Corporate Espionage
Some investigations are tasked with uncovering cases of corporate espionage, where competitors may be attempting to gain access to sensitive information illegally. Corporate espionage poses a severe threat to business operations and competitive standing.
Uncovering and addressing corporate espionage is vital for securing sensitive information and maintaining a competitive edge. Corporate investigations help in identifying spies and preventing unauthorized access to confidential data.
- Investigating cases of corporate espionage.
- Identifying individuals involved in spying activities.
- Preventing unauthorized access to confidential data.
- Securing sensitive information from competitors.
- Maintaining a competitive edge and operational security.
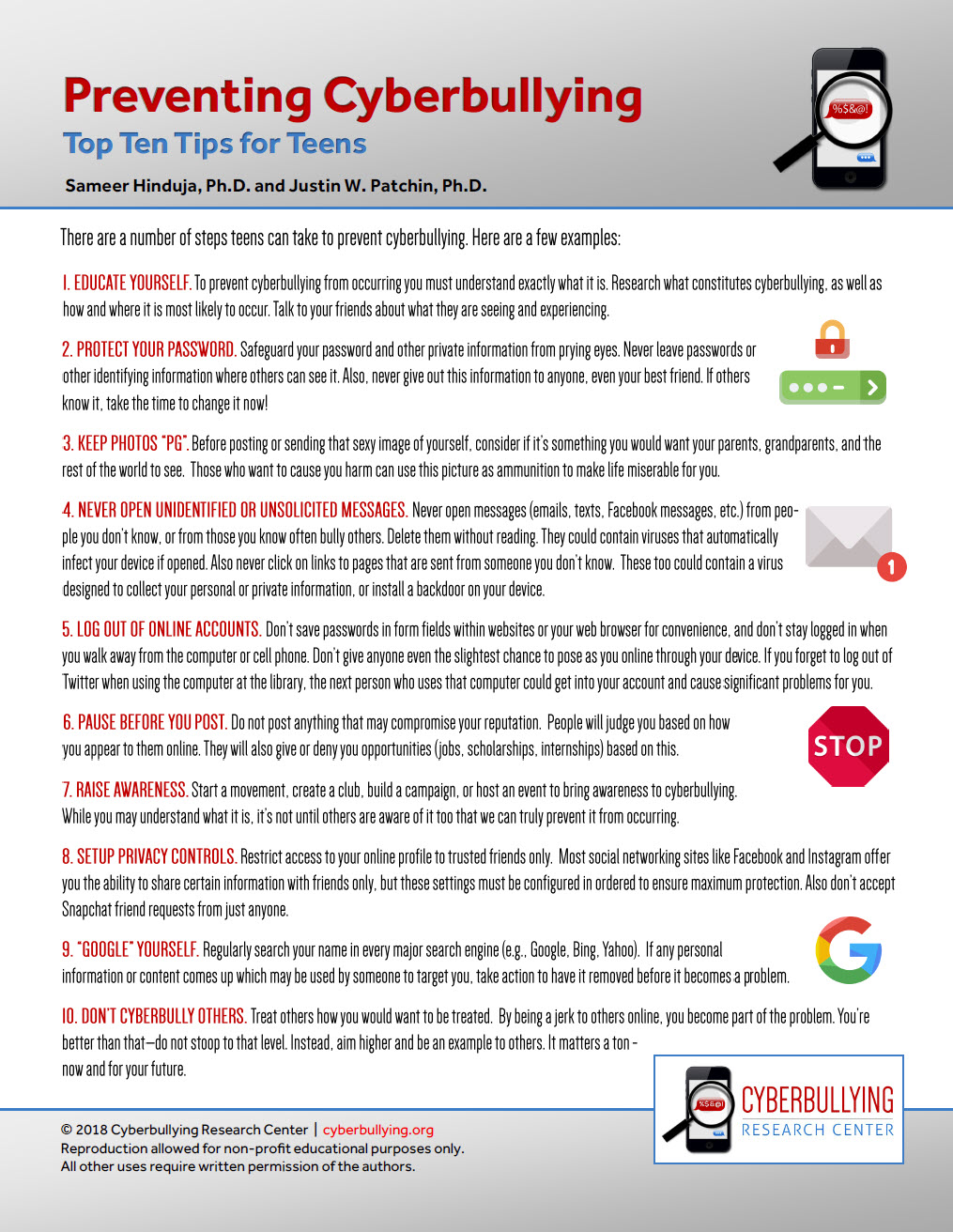
Employee Background Checks
Regular checks of current and potential employees ensure they have the qualifications, experience, and integrity required, helping companies to mitigate risks associated with hiring. Background checks are crucial for verifying employee credentials and history.
Ensuring employees' qualifications and integrity is vital for creating a dependable workforce. Regular background checks help companies avoid hiring individuals with questionable pasts, reducing the risks associated with employee misconduct.
- Conducting regular background checks on employees.
- Ensuring qualifications and integrity of employees.
- Mitigating risks associated with hiring decisions.
- Verifying employee credentials and history.
- Creating a reliable and trustworthy workforce.
What are the Possible Outcomes of a Corporate Investigation?
Identification of Wrongdoing
Corporate investigations can uncover various forms of misconduct, such as fraud, embezzlement, regulatory violations, or unethical behavior within the organization. Identifying these wrongdoings is the first step towards rectifying the issues.
Addressing misconduct promptly is crucial for maintaining the company's ethical standards and operational efficiency. Investigations help in identifying the individuals involved and taking necessary actions to mitigate the impact of their wrongdoing.
- Uncovering cases of fraud and embezzlement.
- Identifying regulatory violations and unethical behavior.
- Taking the first step towards rectifying issues.
- Maintaining company's ethical standards and efficiency.
- Mitigating the impact of identified misconduct.
Legal Consequences
Findings from corporate investigations may lead to legal actions, including lawsuits, fines, or sanctions imposed by regulatory bodies against the individual or corporation involved. Legal consequences ensure accountability and deter future misconduct.
Legal actions restore the company's reputation and emphasize a no-tolerance policy towards unethical behavior. Ensuring accountability among employees and associates helps in creating a more transparent and trustworthy business environment.
- Leading to lawsuits, fines, and sanctions.
- Ensuring accountability for unethical behavior.
- Restoring the company's reputation.
- Deterring future misconduct
- Creating a transparent business environment.
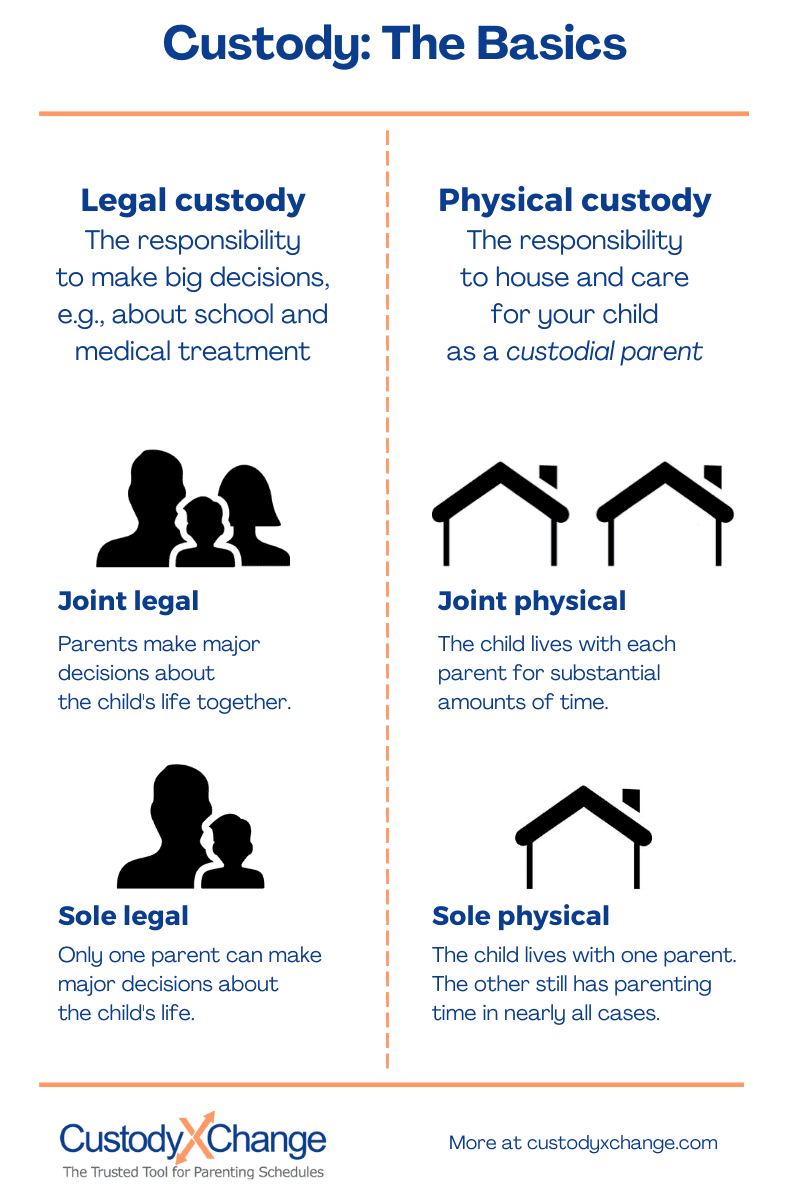
Internal Discipline
The results of the investigation can prompt the company to take internal disciplinary actions, such as terminating or penalizing employees found guilty of misconduct. Internal discipline reinforces the company's commitment to ethical conduct.
Disciplinary actions emphasize the importance of following company policies and ethical guidelines. By addressing misconduct internally, companies can maintain a strong internal culture and prevent future violations.
- Prompting internal disciplinary actions.
- Terminating or penalizing guilty employees.
- Reinforcing commitment to ethical conduct.
- Emphasizing the importance of company policies.
- Maintaining a strong and ethical internal culture.
Policy Revisions
Identifying gaps or weaknesses in current protocols often compels businesses to revise their policies and procedures to prevent future issues. Policy revisions ensure that companies evolve with changing business environments and challenges.
Revamping policies and procedures based on investigation findings helps companies stay proactive in risk management. This continuous improvement approach ensures the company's growth and adaptability to new business challenges.
- Identifying gaps in current protocols.
- Revising policies to prevent future issues.
- Ensuring evolution with changing environments.
- Staying proactive in risk management.
- Promoting continuous improvement and growth.
Reputational Impact
Depending on the nature and severity of the findings, a corporate investigation can significantly impact the company's reputation, influencing public perception and stakeholder confidence. Addressing issues promptly helps restore trust and integrity.
Maintaining a good reputation is essential for a company's success. Corporate investigations help in addressing and resolving issues that could tarnish the company's image.
Wrapping up Corporate Investigations
Corporate investigations are essential for uncovering internal and external threats, including fraud, embezzlement, and corporate espionage. Private investigators specialize in gathering evidence, conducting interviews, and performing surveillance to support corporate investigations.
These professionals ensure that companies can address violations of policies or laws effectively, securing their assets and reputations. Utilizing private investigators can help businesses maintain regulatory compliance and prevent financial losses.
- Uncovering internal and external threats.
- Gathering evidence and conducting interviews.
- Performing surveillance to support investigations.
- Addressing policy and legal violations effectively.
- Securing company assets and reputation.
Employing expert investigators provides a confidential and objective approach to resolving complex corporate issues. Their expertise ensures that investigations are thorough and unbiased, leading to credible and actionable findings that can guide the company's next steps.
- Providing a confidential approach to investigations.
- Ensuring objective and unbiased findings.
- Resolving complex corporate issues effectively.
- Guiding the company's next steps with actionable insights.

Connect with us today to safeguard your business. Call Taylor Payton Investigations at 844-426-6370 or visit TaylorPayton.com for more information on how our services can benefit you.
]]>